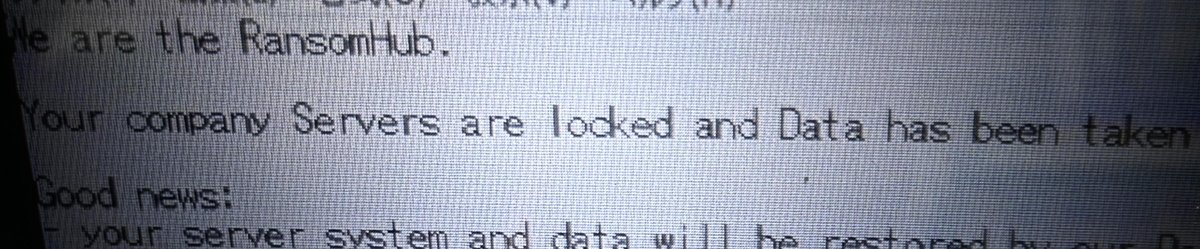
A message left by RansomHub on a dairy company’s system
2:00 JST, March 15, 2026
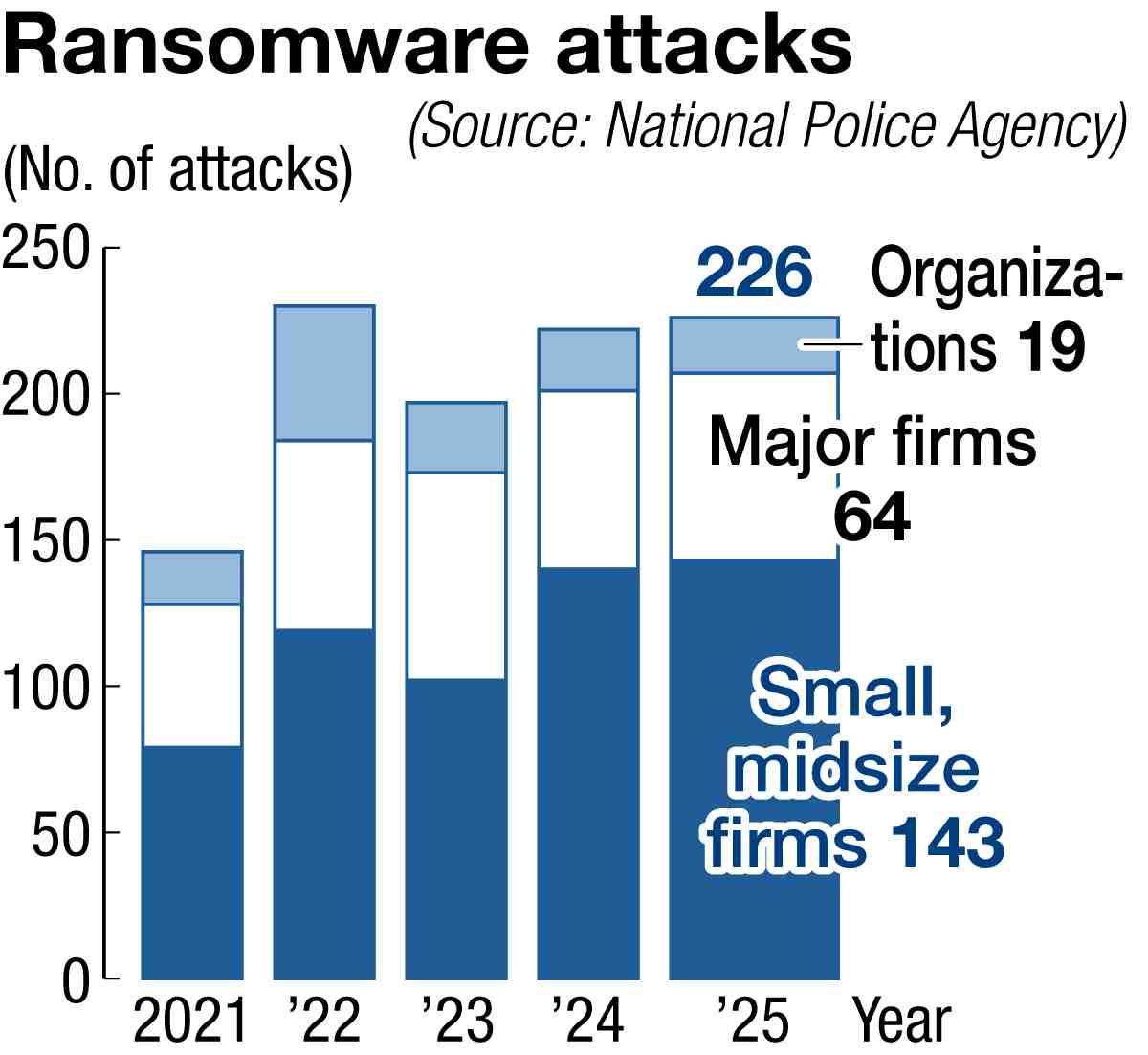
Last year saw 143 ransomware attacks on small and midsize companies in Japan, accounting for 60% of all attacks in the country for the second year in a row, according to the National Police Agency.
Officials at one company that was targeted said the attack could have caused the firm’s bankruptcy.
Data hacked
Early on the morning of Jan. 6 last year, a security official at a manufacturer of dairy products in Tokyo received an automated call that said irregularities had been detected in the company’s internal system. Accessing the server via a computer at home, he found that some file extensions had been overwritten.
“Is this ransomware?” he thought. After instructing all employees via the in-company chat not to start their computers, he rushed to his firm’s data center.
There, he discovered that almost all their data had been encrypted. When he opened a text file on the server that had been left unencrypted, he saw that it was a note from RansomHub, a notorious ransomware group, that claimed responsibility and said the data had been “taken” to the group’s server.
Brought to a standstill
Data about the firm’s roughly 7,000 corporate customers and personal information about its employees was encrypted and a server at a separate location was also affected. The firm was forced to suspend production and distribution. Even the backup files, which were supposed to have been impossible to overwrite, had been encrypted.
The ransomware group demanded a payment of $1 million, or about ¥150 million, to restore the data. Management decided that same day not to comply with the demand, believing the data might not be restored even if they paid. The company’s headquarters ground to a halt.
But there was one saving grace. The firm’s core system, which had a specially designed operating system, had not been attacked. The system was introduced about 40 years ago and was set to be retired in about six months.
The core system was accessed safely from a computer, suggesting it might be possible to take some orders and check stock again.
It was around 3 p.m. that the firm managed to partially resume operations. The company explained the situation to customers over the phone and received orders via phone and fax. The firm continued production with rough projections, keeping its plants online.
Early warning signs
The company was hacked through a virtual private network, or VPN, which was used to access the in-company system from outside. The company identified traces of an attack three days before, but it was unable to decrypt files in the attacked server. It took the firm four months to completely restore operations, costing it tens of millions of yen, including for safety measures after the incident.
So far, there is no sign of secondary damage, such as the disclosure of customer information.
“The attack was beyond our expectations,” said one corporate official. “The incident made us keenly aware that we need a system that will allow us to keep operating even if it gets infected or we are attacked, which could mean a backup system that is not connected to the internet.”
“We never expected our firm would be targeted,” said a senior official. “The core system just happened to survive, but otherwise we would have gone bankrupt.”
Top Articles in Business
-

Nippon Life Insurance’s U.S. Arm Sues OpenAI Over Legal Assistance Provided by ChatGPT
-

Japan, U.S. Name 3 Inaugural Investment Projects; Reached Agreement After Considerable Difficulty
-

Japan’s Major Real Estate Firms Expanding Overseas Businesses to Secure Future Growth, Focusing on Europe, U.S., Asia
-

JR Tokai Breaks Ground on Yamanashi Maglev Station; Will Be Part of Linear Chuo Shinkansen Line from Tokyo to Nagoya
-

Transport Companies See Opportunity in Narita Expansion; Airlines, Railways Prepare to Meet Expected Growth in Demand
JN ACCESS RANKING
-

Producer Behind Pop Group XG Arrested for Cocaine Possession
-

Japan PM Takaichi’s Cabinet Resigns en Masse
-

Man Infected with Measles Reportedly Dined at Restaurant in Tokyo Station
-
Videos Plagiarized, Reposted with False Subtitles Claiming ‘Ryukyu Belongs to China’; Anti-China False Information Also Posted in Japan
-

Japan Figure Skating Legend Yuzuru Hanyu Is Proud Disaster Survivor and Gold Medalist, Vows to Continue Support Efforts