16:25 JST, May 3, 2021
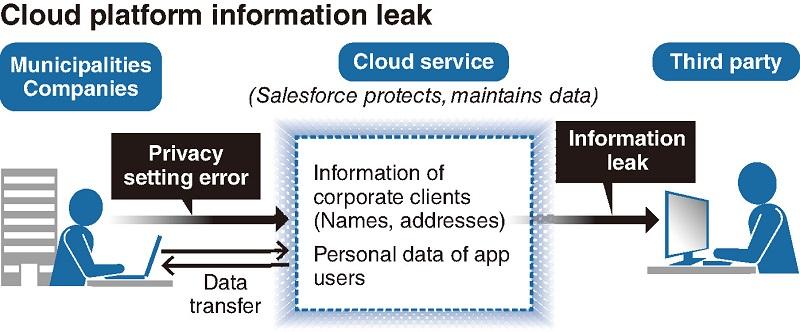
Platform interface issues in a cloud system provided by a U.S. contractor exposed the personal information stored by dozens of municipalities and companies in Japan to unauthorized viewers, after users mistakenly configured the system’s settings to allow public access to their content.
Local governments and corporate users maintain that they chose the wrong settings due to the overly complicated nature of the system.
Warning that there may be even more companies who have similarly misconfigured their settings with the service, the National center of Incident readiness and Strategy for Cybersecurity (NISC) has asked the U.S. provider to remedy the situation.
Domestic giant affected
The service was provided by U.S.-based IT company Salesforce.com, Inc., whose Japanese subsidiary, Salesforce.com Co., is one of the leading names in cloud storage in Japan.
According to the Internal Affairs and Communications Ministry and the Personal Information Protection Commission, the data of 20 local governments, including the Funabashi and Ibaraki city governments, and 18 companies, including Rakuten Group Inc. and SMBC Nikko Securities Inc., was left accessible to unintended eyes. In all cases, the municipalities and companies had mistakenly set their privacy settings to allow public viewing.
The data of seven cities, including Kobe and Higashi-Murayama, and five companies, including Rakuten and SoftBank Group Corp.’s cashless payment service provider PayPay Corp., were found to have been accessed by outside parties, although it remains unknown whether the personal information was abused after being viewed.
The breaches came to light after PayPay announced in December that the names and contact information of its member store owners had been compromised. Later that month, Rakuten similarly announced that over 1.48 million sets of names and contact information, including those who had requested information on setting up an online shop with the cybermall had been exposed, and confirmed that it had found evidence that at least some of the datasets had been viewed by third-parties.
600-page instructions
Although Salesforce and other cloud computing service providers handle all of the back-end architecture for clients, it is up to the users to configure their privacy settings and access authorizations on the front end.
“It’s not that our company has flaws in our products, but that our clients misconfigured their access authorizations,” said a Salesforce spokesperson.
But the companies and local government offices that contract with Salesforce contend that their service is far from user-friendly.
“Just to identify where the problem was with our settings, we would have to read over 600 pages of instructions,” said an employee at an affected financial institution. “The company needs to provide more support.”
In January, Rakuten issued a statement, saying: “We have continued to ask the system provider for detailed information on specification changes and reconfigurations.”
Top Articles in Business
-

Foreign Tourists Set New Record in March; 30% Drop in Visitors from Middle East
-

Japan’s ANA to Introduce Fuel Surcharges to Domestic Flights from Fy27, Driven by Rising Fuel Costs, Declining Profits
-

Toyota Motor to Begin Full-Scale Hydrogen Production in May; Mass Production and Sales of Equipment Planned to Start in 2029
-

Middle Powers Should Create Alternative to WTO, Says Research Group
-

Airborne Cellular Stations to Be Tested in Ishikawa, Miyagi; Aim to Ensure Communication During Disasters
JN ACCESS RANKING
-

Earthquake Hits Japan’s Tohoku Region; 3-meter Tsunami Warning Issued (Update 1)
-

Police Find Child’s Shoe During Search for Missing Boy in Nantan, Kyoto Prefecture
-

Body Found in Nantan, Kyoto Prefecture, During Search for 11-Year-Old Boy in Area (Update 1)
-

China, South Korea Object to Japanese PM Takaichi’s Ritual Offering to Yasukuni Shrine
-

Cherry Blossoms, Rapeseed Flowers Perform Colorful ‘Duet’ in Niigata
Most read in the last 24 hours
-
Iran's Top Diplomat Briefly Returns to Pakistan but Trump Says th...
-

DC Gala Shooting Suspect Aired Grievances against Trump in Writin...
-

Tokyo Vice Governor: SusHi Tech Tokyo Garners Tangible Business O...
-

M6.1 Earthquake Hits Hokkaido, Japan; No Tsunami Expected
-

Japan to Host Leaders from Major Cities from Around the World for...
Most read in the last 7 days
-

China, South Korea Object to Japanese PM Takaichi's Ritual Offeri...
-

Trump Extends the Ceasefire with Iran but Keeps the Blockade
-

India's Arms Indigenization Quest for Self-Reliance / New Delhi S...
-

¥1,000 Coins to Be Issued to Mark Anniversary of Beginning of Jap...
-

Most Serious Cyberattacks against the UK Now from Russia, Iran an...
Most read in the last 30 days
-

Earthquake Hits Japan's Tohoku Region; 3-meter Tsunami Warning Is...
-

Police Find Child's Shoe During Search for Missing Boy in Nantan,...
-

Body Found in Nantan, Kyoto Prefecture, During Search for 11-Year...
-

China, South Korea Object to Japanese PM Takaichi's Ritual Offeri...
-

Cherry Blossoms, Rapeseed Flowers Perform Colorful ‘Duet’ in Niig...